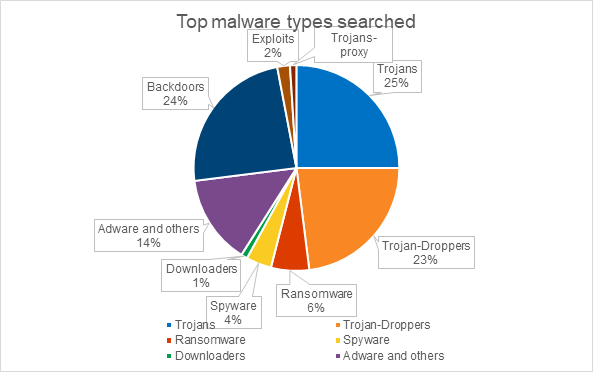
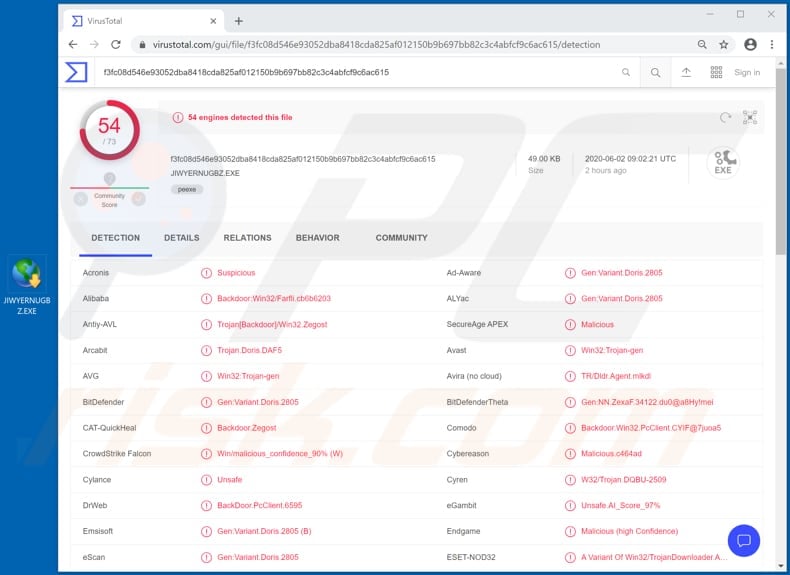
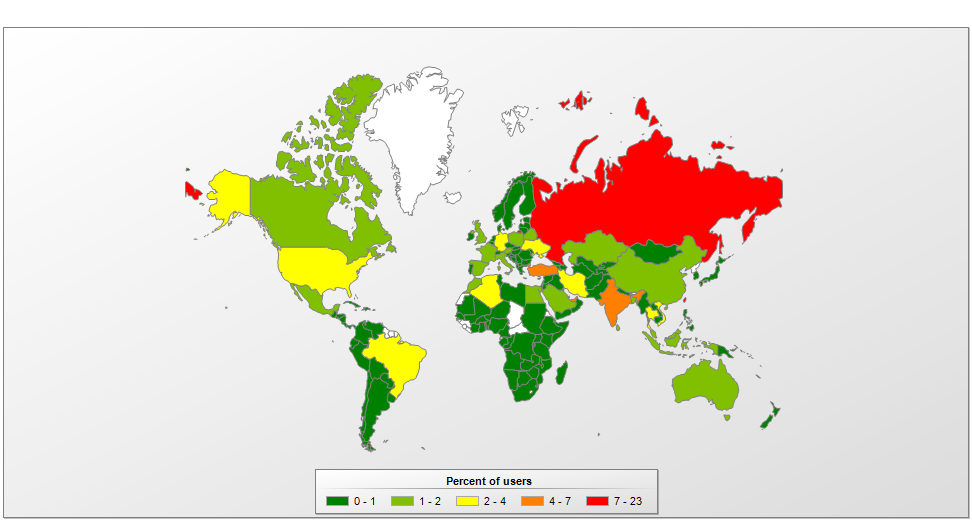
Kaspersky security analysts
 PPT - Virus/ Trojans/ Worms etc and
PPT - Virus/ Trojans/ Worms etc and  Trojan and Virus,Trojan horse,virus,how
Trojan and Virus,Trojan horse,virus,how  SPYWARE AND TROJAN HORSE INFECTIONS
SPYWARE AND TROJAN HORSE INFECTIONS  What is a Trojan virus? How this tricky
What is a Trojan virus? How this tricky  viruses, trojans and malicious software
viruses, trojans and malicious software  Network Security, Malicious Threats
Network Security, Malicious Threats  9 types of malware and how to recognize
9 types of malware and how to recognize  Infected with Viruses, Malware
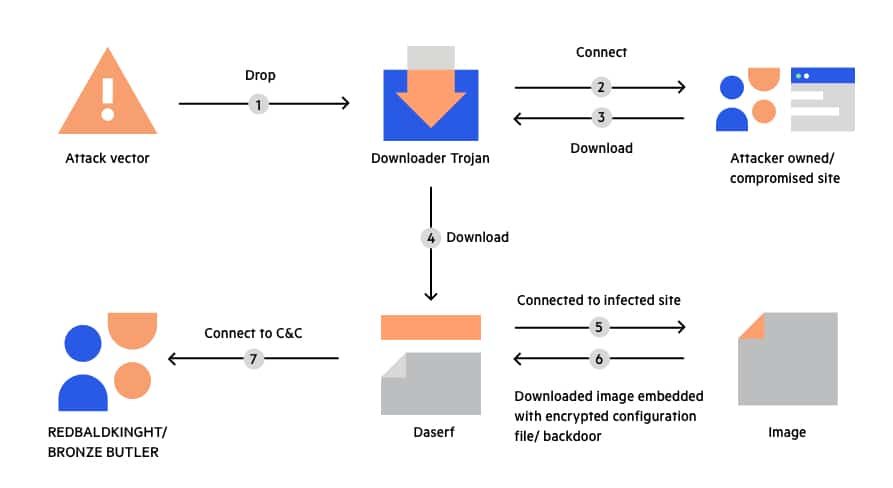
Infected with Viruses, Malware  Trojans, Backdoors and Droppers: The
Trojans, Backdoors and Droppers: The  Definition of a Trojan Virus | Computer
Definition of a Trojan Virus | Computer  Worms, Trojans \u0026 Bots – Understanding
Worms, Trojans \u0026 Bots – Understanding  Hacking #Linux #KaliLinux #rootsector
Hacking #Linux #KaliLinux #rootsector  The 11 Most Common Types of Malware and
The 11 Most Common Types of Malware and  Financial Services: Banking Trojans
Financial Services: Banking Trojans  Research interest: Trojans, Backdoors
Research interest: Trojans, Backdoors 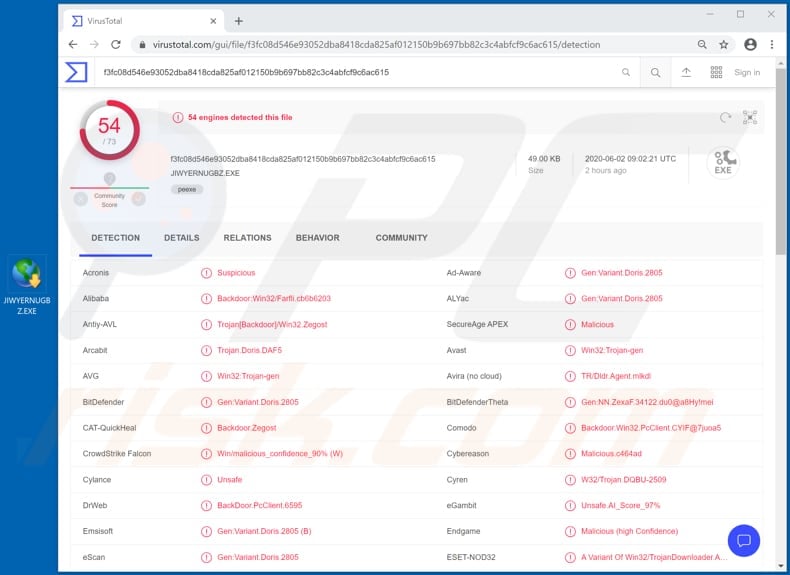 How to remove Dupzom Trojan - virus
How to remove Dupzom Trojan - virus 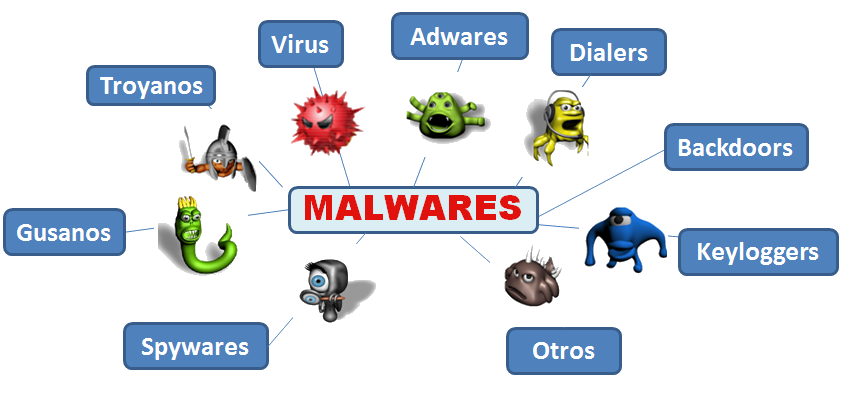 should know about computer security threats
should know about computer security threats  Torjan horse virus
Torjan horse virus  Trojan Horse Virus Symptoms | How to
Trojan Horse Virus Symptoms | How to  Cyber Security Attacks – Techlifezine
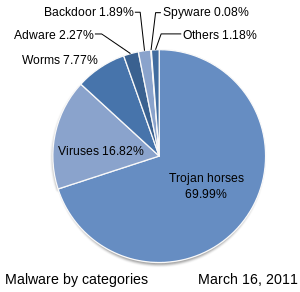
Cyber Security Attacks – Techlifezine 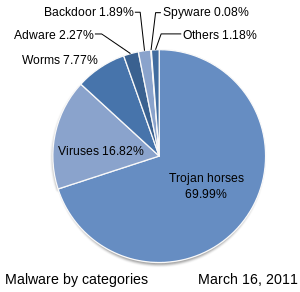 Malware - Wikipedia
Malware - Wikipedia  Malware, Rootkits, and Trojans
Malware, Rootkits, and Trojans  What is malware? A guide to the 12 most
What is malware? A guide to the 12 most  Torjan horse virus
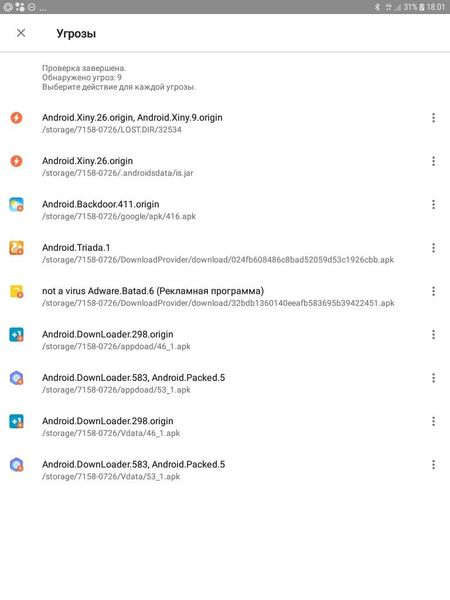
Torjan horse virus 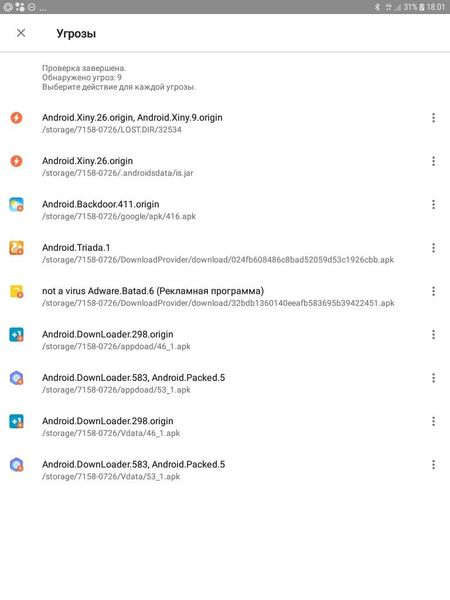 How many Trojans can one smart phone hold?
How many Trojans can one smart phone hold?  PDF) A Cyber Kill Chain Based Analysis
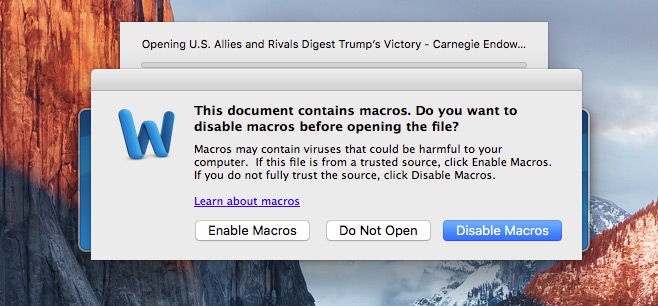
PDF) A Cyber Kill Chain Based Analysis 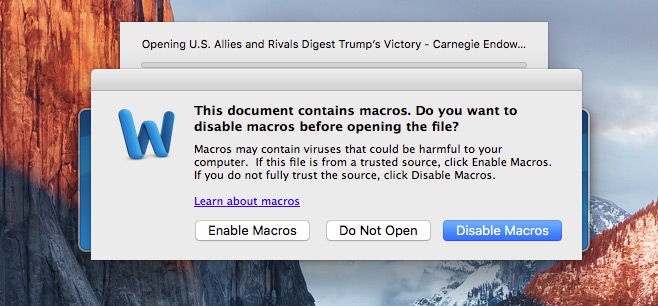 Word file exploit discovered
Word file exploit discovered  Common Malware Types: Vulnerability
Common Malware Types: Vulnerability  Bravo Hackers - Posts | Facebook
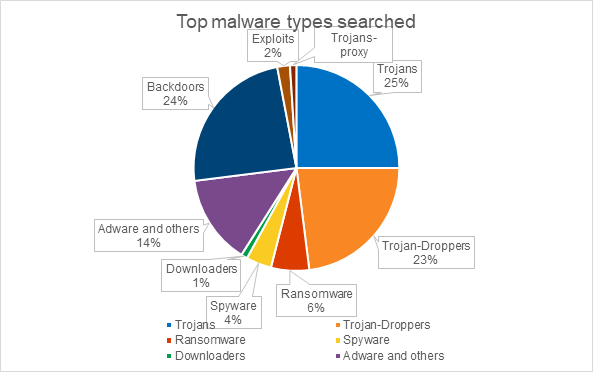
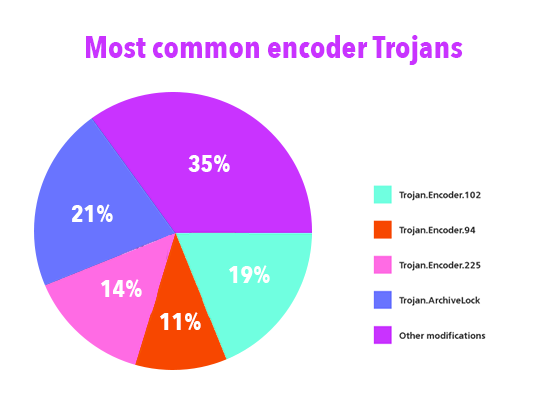
Bravo Hackers - Posts | Facebook  IT threat evolution Q3 2019. Statistics
IT threat evolution Q3 2019. Statistics  Different Examples of a Trojan Horse
Different Examples of a Trojan Horse 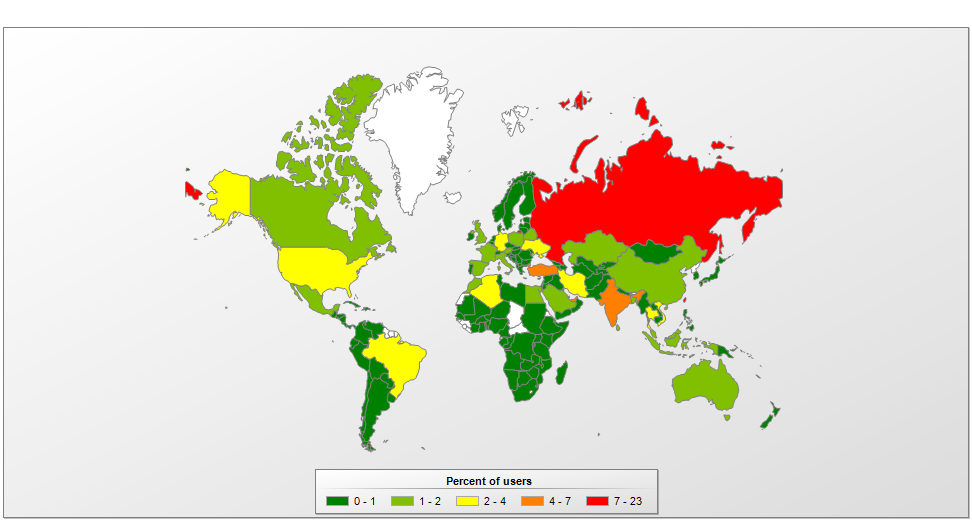 Kaspersky Threats — Neurevt
Kaspersky Threats — Neurevt  Common types of cybersecurity attacks
Common types of cybersecurity attacks
Austria's Presidential Election Could Shock Europe common trojans Dadaab: Kenya to Close The World’s Biggest Refugee Camp common trojans Chilcot: Jeremy Corbyn Apologizes for Iraq War common trojans Why Has Obama Lifted the Arms Sales Ban on Vietnam common trojans
common trojans Gold White Black Red Blue Beige Grey Price Rose Orange Purple Green Yellow Cyan Bordeaux pink Indigo Brown Silver































:max_bytes(150000):strip_icc()/GettyImages-147215503-7e202a7619544efb9e6ed1bb41c00787.jpg)