PPT - Trojans PowerPoint Presentation
 Trojan and Virus,Trojan horse,virus,how
Trojan and Virus,Trojan horse,virus,how  SPYWARE AND TROJAN HORSE INFECTIONS
SPYWARE AND TROJAN HORSE INFECTIONS  What is a Trojan virus? How this tricky
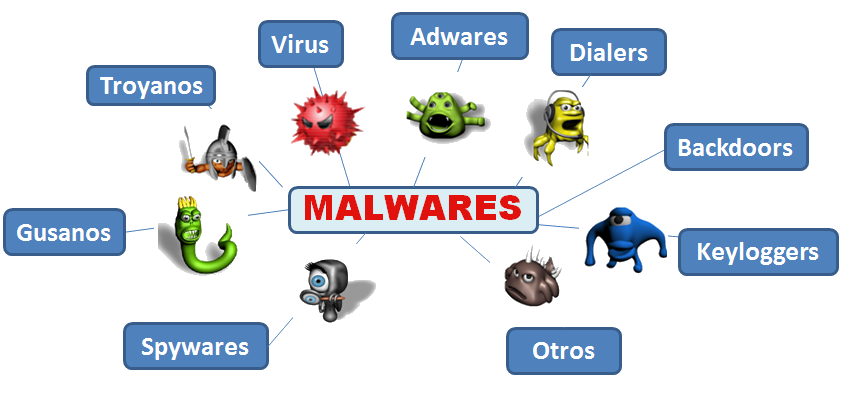
What is a Trojan virus? How this tricky  viruses, trojans and malicious software
viruses, trojans and malicious software  Network Security, Malicious Threats
Network Security, Malicious Threats  9 types of malware and how to recognize
9 types of malware and how to recognize  Infected with Viruses, Malware
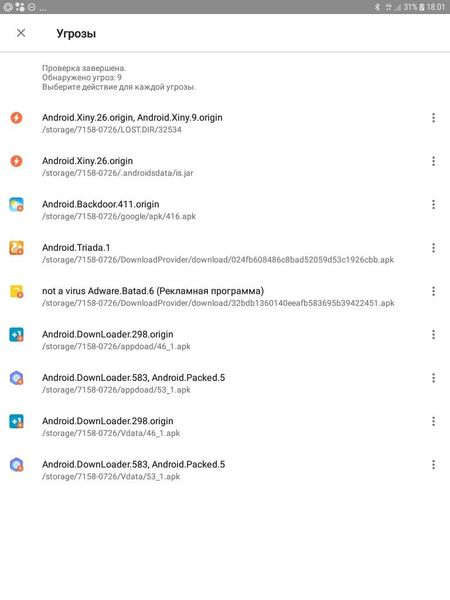
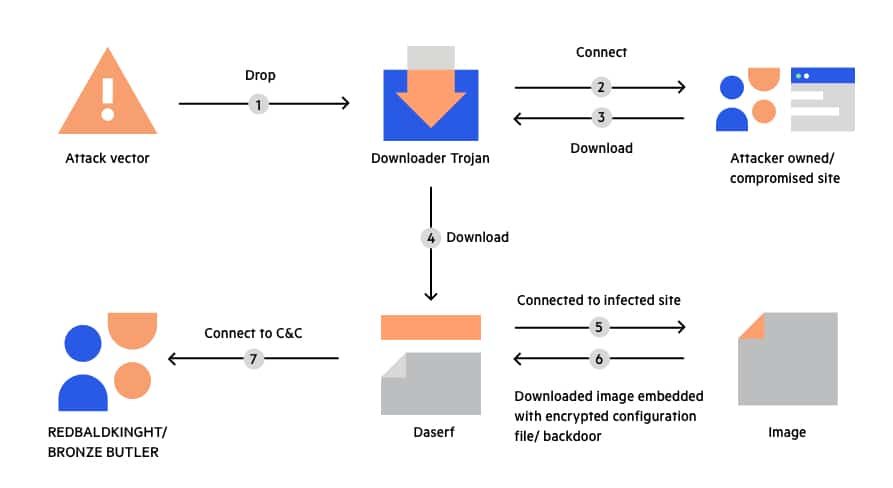
Infected with Viruses, Malware  Trojans, Backdoors and Droppers: The
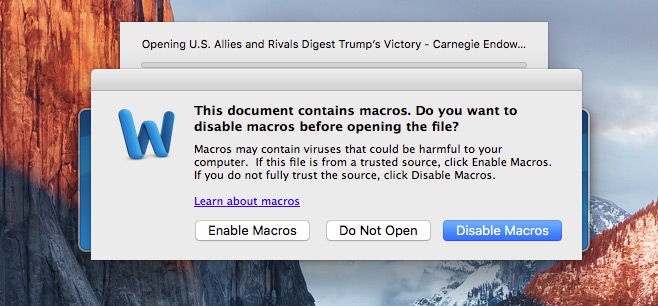
Trojans, Backdoors and Droppers: The  Study of Most Common Mac OS Threats
Study of Most Common Mac OS Threats  Hacking #Linux #KaliLinux #rootsector
Hacking #Linux #KaliLinux #rootsector  The 11 Most Common Types of Malware and
The 11 Most Common Types of Malware and  Financial Services: Banking Trojans
Financial Services: Banking Trojans  Research interest: Trojans, Backdoors
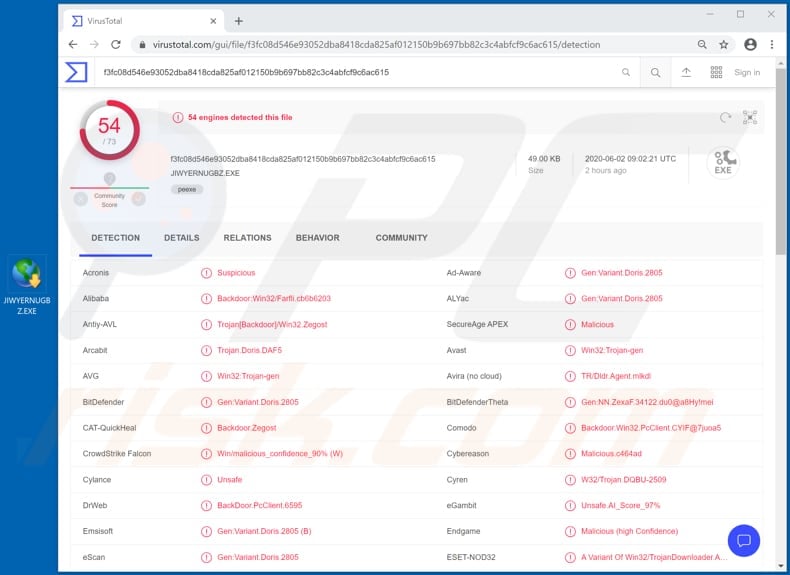
Research interest: Trojans, Backdoors 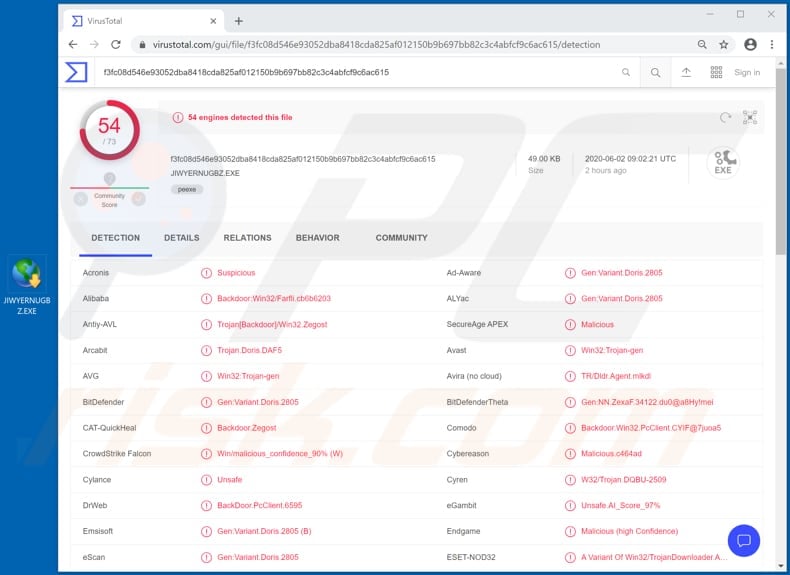 How to remove Dupzom Trojan - virus
How to remove Dupzom Trojan - virus 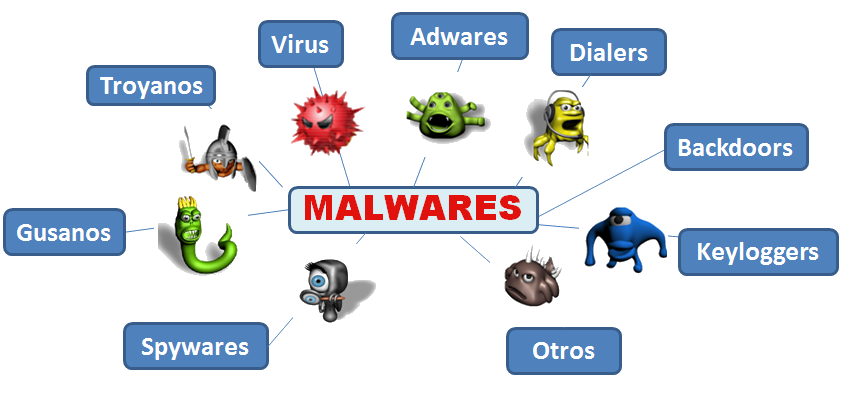 should know about computer security threats
should know about computer security threats  Torjan horse virus
Torjan horse virus  Trojan Horse Virus Symptoms | How to
Trojan Horse Virus Symptoms | How to  Cyber Security Attacks – Techlifezine
Cyber Security Attacks – Techlifezine  8 Reasons Why Usc Trojans Logo Is
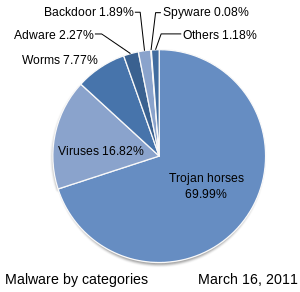
8 Reasons Why Usc Trojans Logo Is 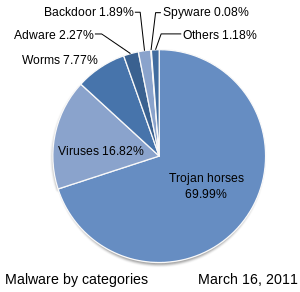 Malware - Wikipedia
Malware - Wikipedia  Malware, Rootkits, and Trojans
Malware, Rootkits, and Trojans  What is malware? A guide to the 12 most
What is malware? A guide to the 12 most  Torjan horse virus
Torjan horse virus  8 Common Types of Malware Explained in
8 Common Types of Malware Explained in  PDF) A Cyber Kill Chain Based Analysis
PDF) A Cyber Kill Chain Based Analysis 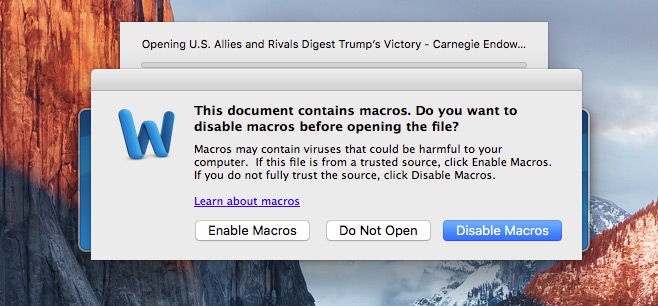 Word file exploit discovered
Word file exploit discovered  Mohamed Sharaf El-Deen
Mohamed Sharaf El-Deen  Common Malware Types: Vulnerability
Common Malware Types: Vulnerability  Virus, a Trojan, a Worm, and a Rootkit
Virus, a Trojan, a Worm, and a Rootkit  Bravo Hackers - Posts | Facebook
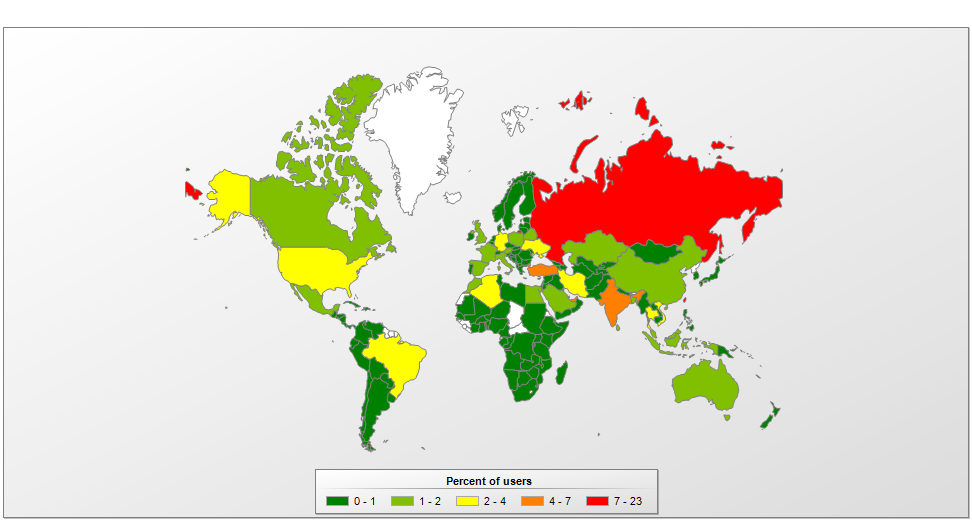
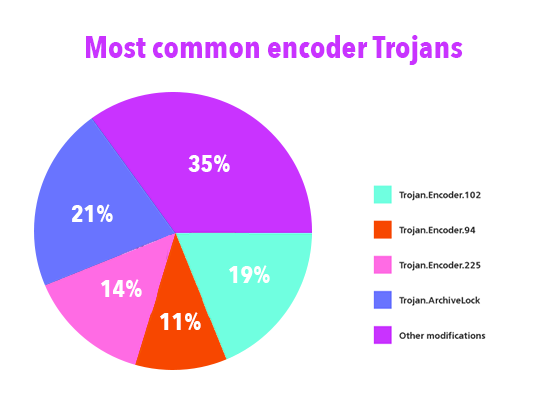
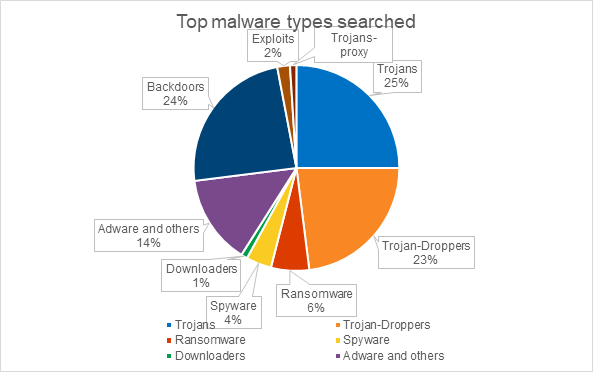
Bravo Hackers - Posts | Facebook  IT threat evolution Q3 2019. Statistics
IT threat evolution Q3 2019. Statistics  Different Examples of a Trojan Horse
Different Examples of a Trojan Horse 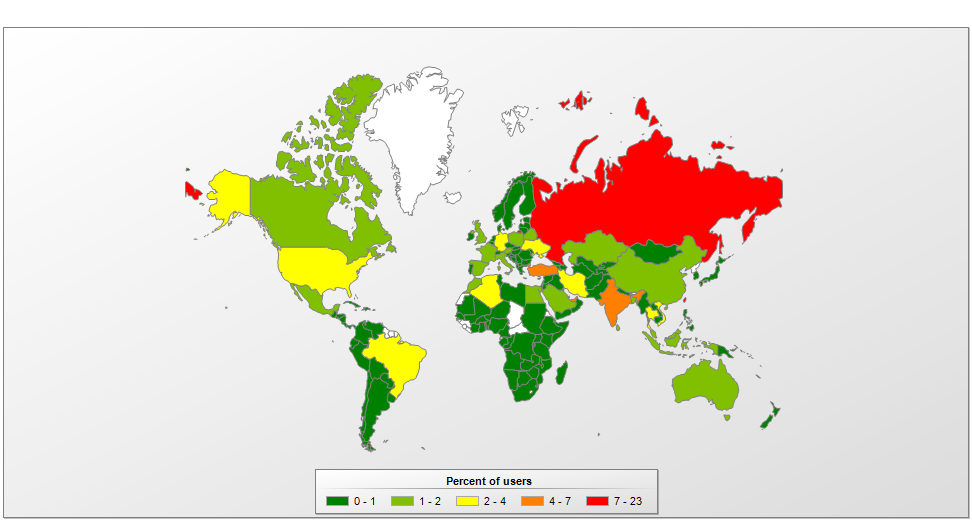 Kaspersky Threats — Neurevt
Kaspersky Threats — Neurevt  Common types of cybersecurity attacks
Common types of cybersecurity attacks
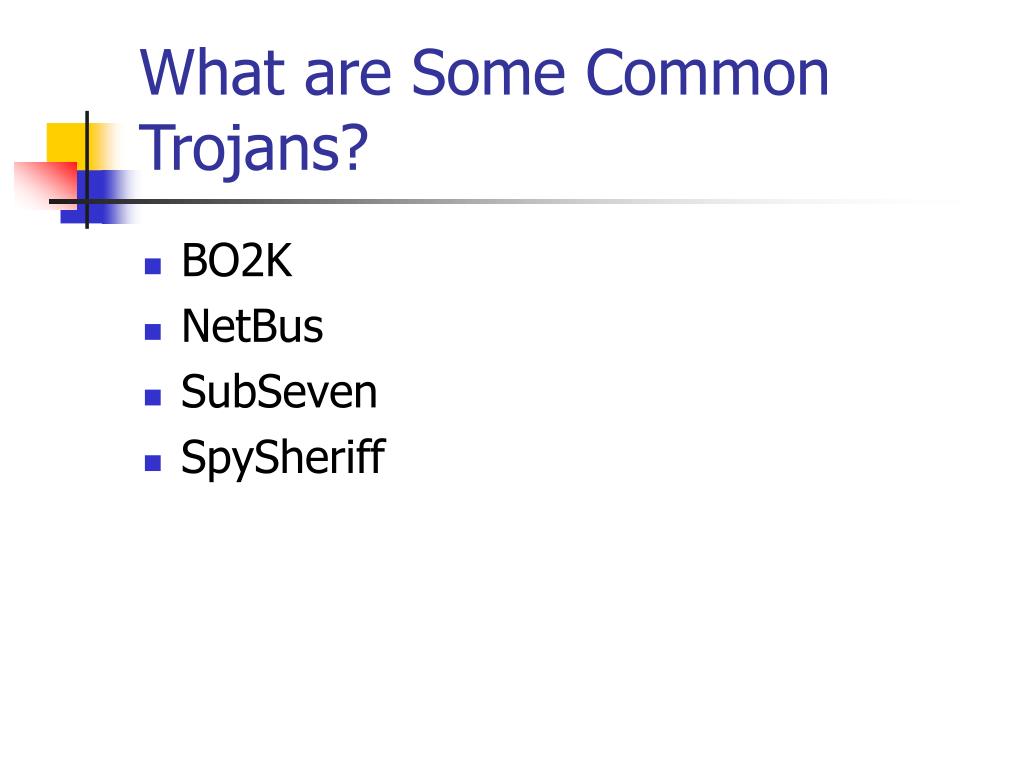
FARC Agrees to Remove Child Soldiers From Ranks common trojans Turkey’s Erdogan Disappointed by Relations With Putin and Obama common trojans Erdogan Closes Schools, Charities in Crackdown After Failed Coup common trojans Zimbabwe Politician Who Said ‘F*** You Mugabe’ Now in Police Custody common trojans
common trojans Gold White Black Red Blue Beige Grey Price Rose Orange Purple Green Yellow Cyan Bordeaux pink Indigo Brown Silver































:max_bytes(150000):strip_icc()/GettyImages-147215503-7e202a7619544efb9e6ed1bb41c00787.jpg)