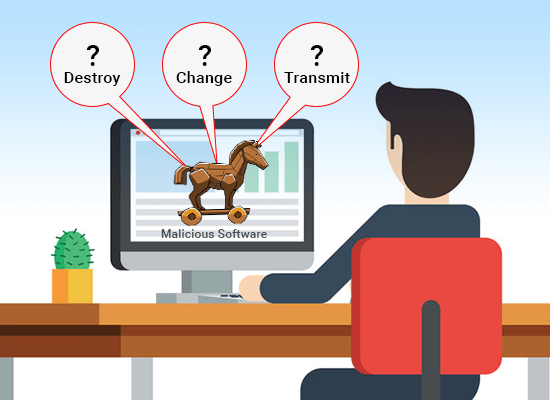
Trojan Attacks | How Does Trojan Horse
 mal-ware cyber security attack Vector Image
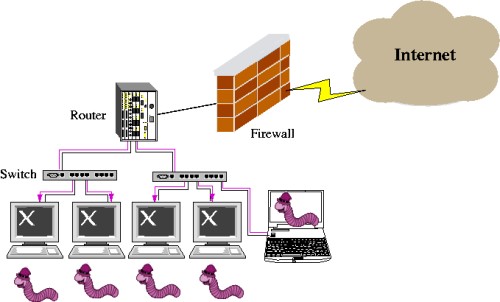
mal-ware cyber security attack Vector Image 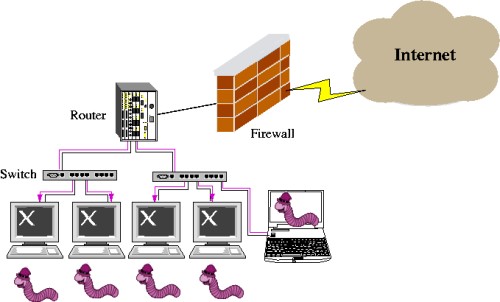 CCNA Security: Worm, Virus and Trojan
CCNA Security: Worm, Virus and Trojan  What is a Trojan Horse Virus? | How to
What is a Trojan Horse Virus? | How to  Trojan Horse Virus Infect Smartphone
Trojan Horse Virus Infect Smartphone  What is a Trojan Horse Virus
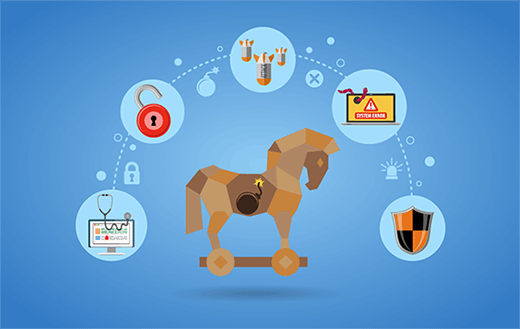
What is a Trojan Horse Virus  What Is Trojan Virus? | How To Protect
What Is Trojan Virus? | How To Protect  Trojan Horse Virus Mal-ware Cyber
Trojan Horse Virus Mal-ware Cyber  What is a Trojan Horse malware - how to
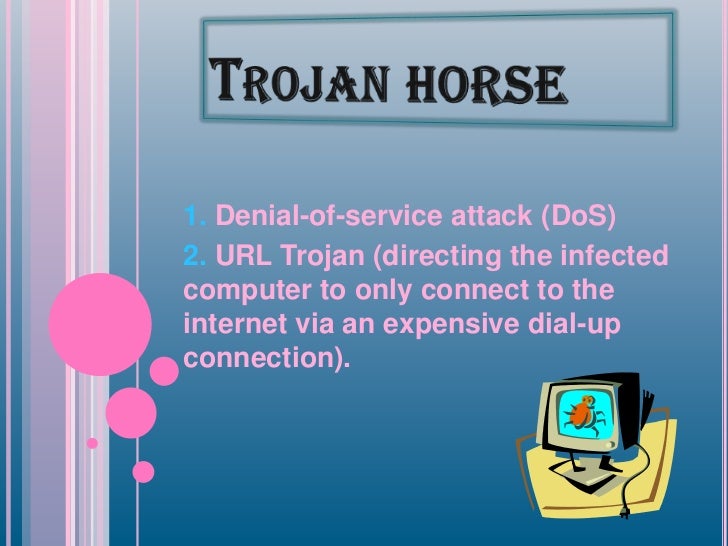
What is a Trojan Horse malware - how to  Distributed Denial of Service Attacks
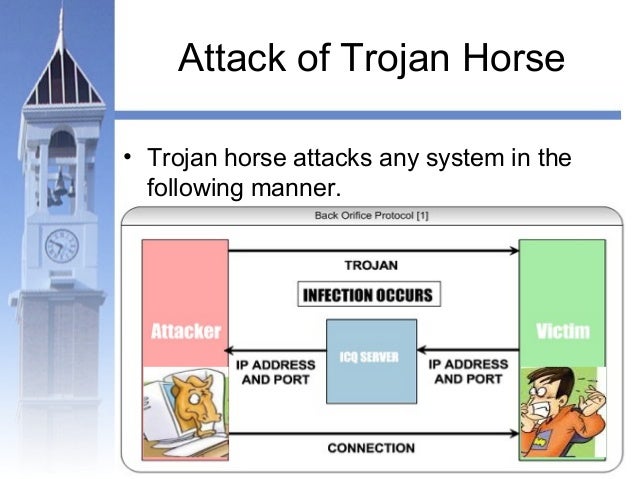
Distributed Denial of Service Attacks  Trojan Horse Virus Attacks
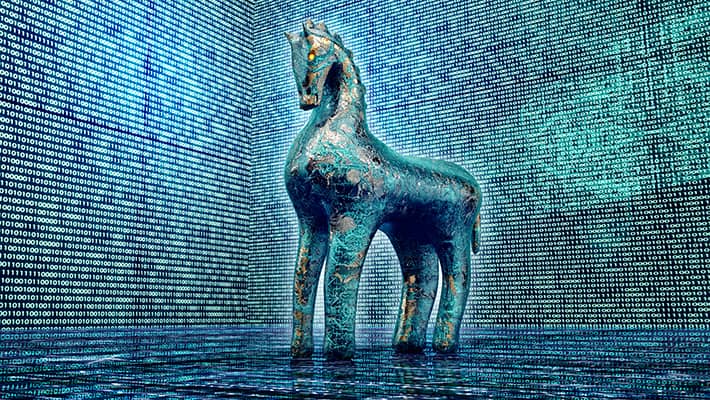
Trojan Horse Virus Attacks  Trojan Virus High Resolution Stock
Trojan Virus High Resolution Stock 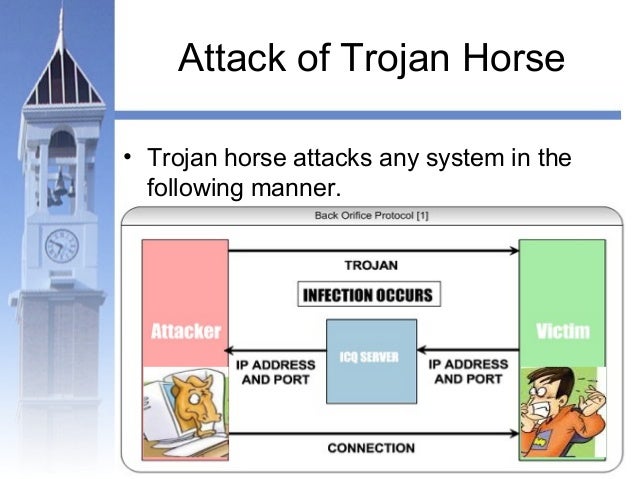 Malicious
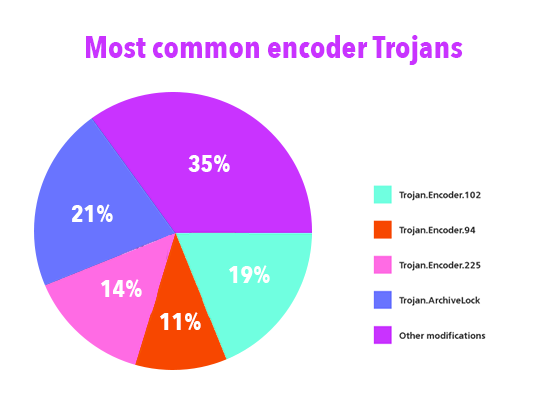
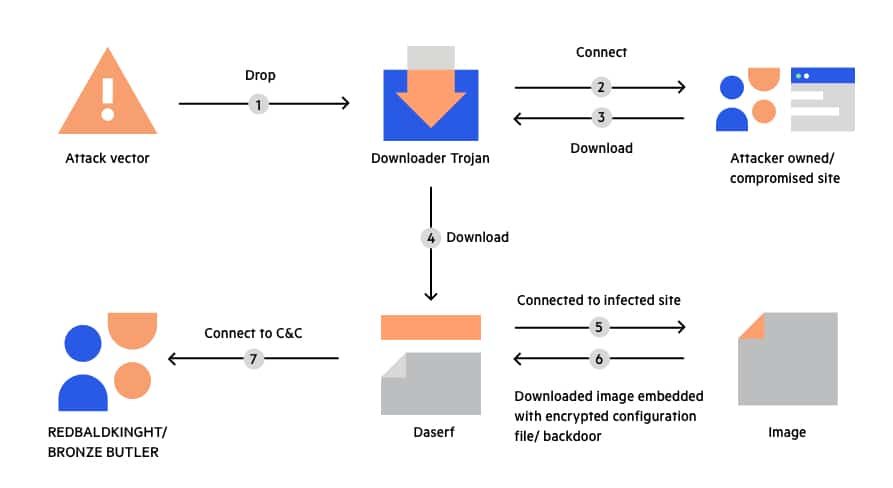
Malicious 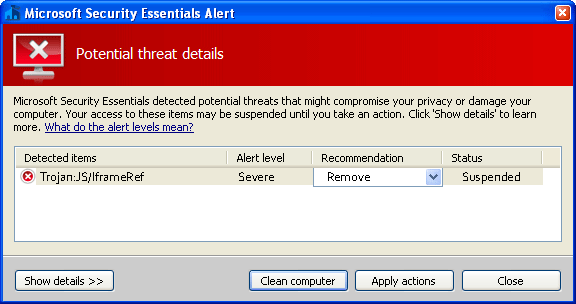 Types of Trojan Attacks 2015. Network
Types of Trojan Attacks 2015. Network 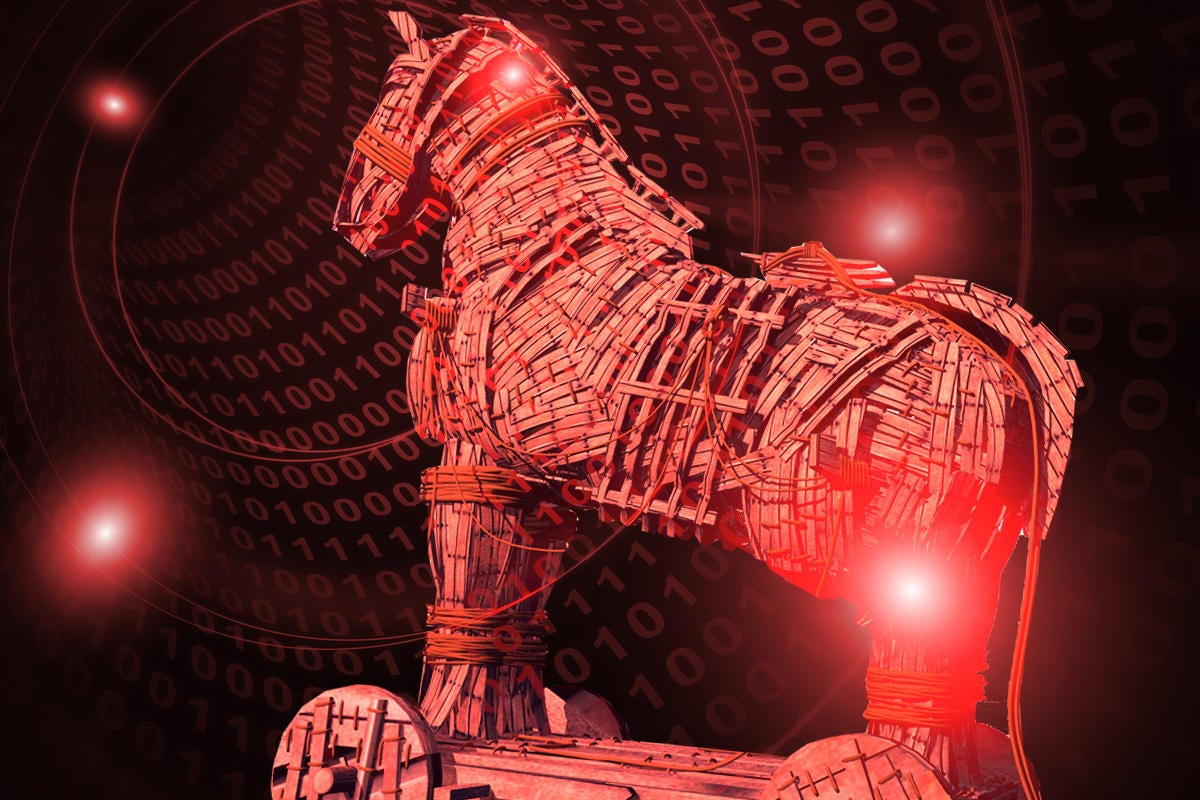 What is a Trojan virus? How this tricky
What is a Trojan virus? How this tricky 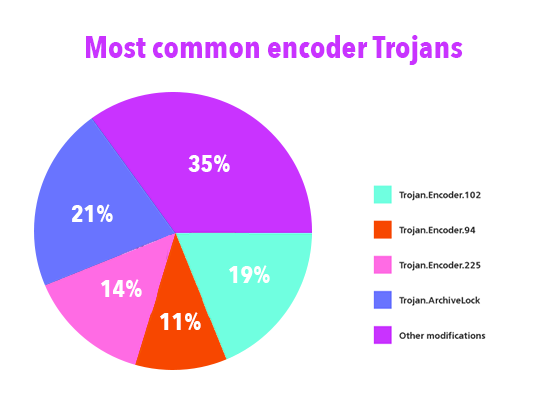 Common Trojan Viruses | How to Remove
Common Trojan Viruses | How to Remove  What is a Trojan Horse malware - how to
What is a Trojan Horse malware - how to  Trojan attack
Trojan attack  How Trojan Horses Work | HowStuffWorks
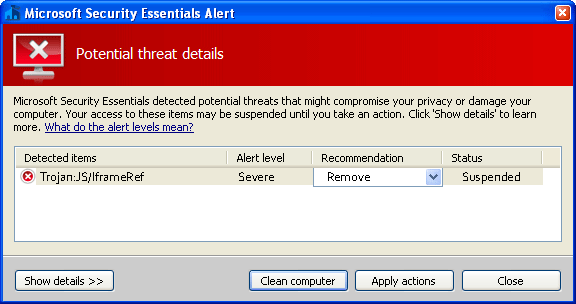
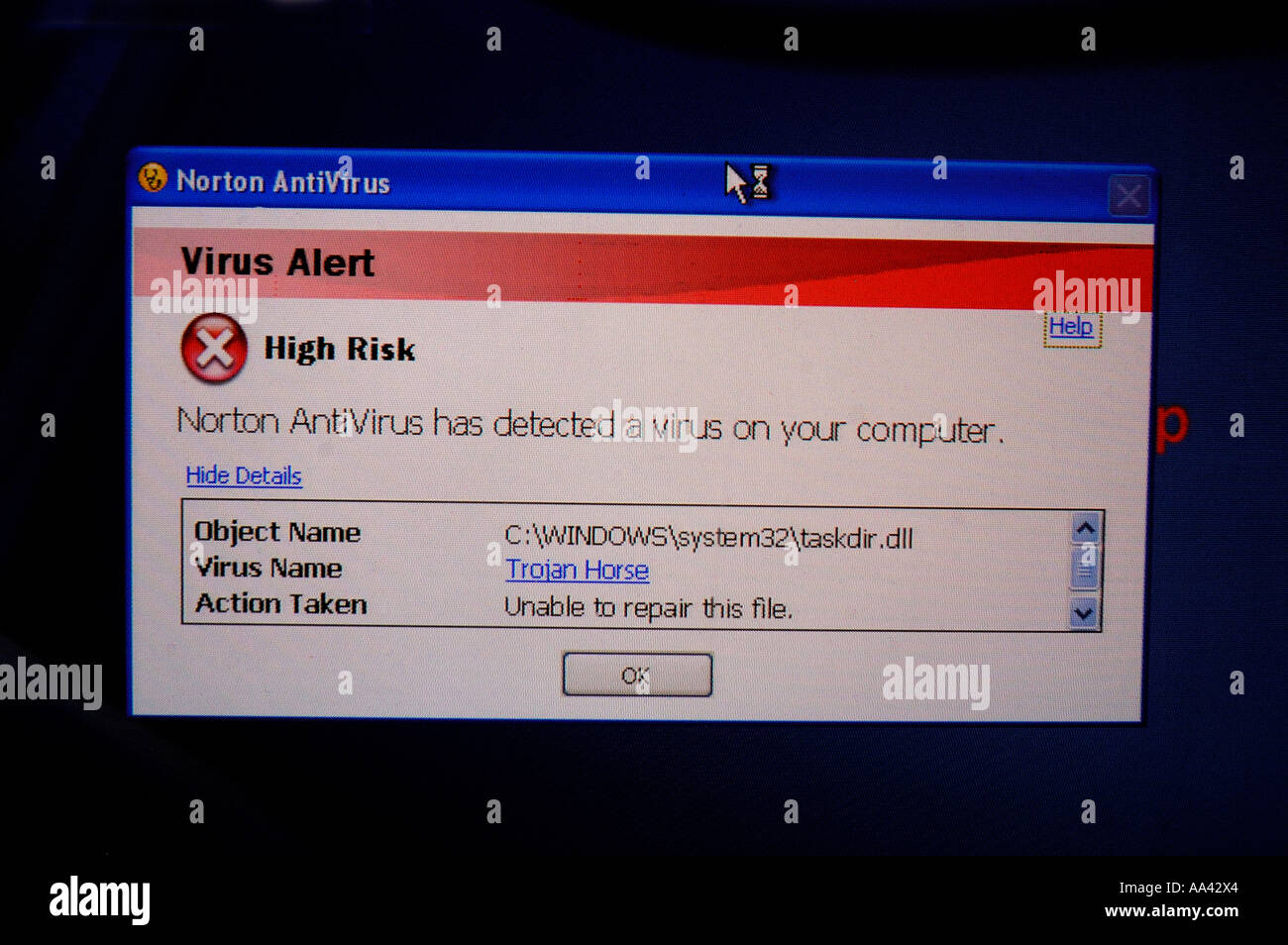
How Trojan Horses Work | HowStuffWorks 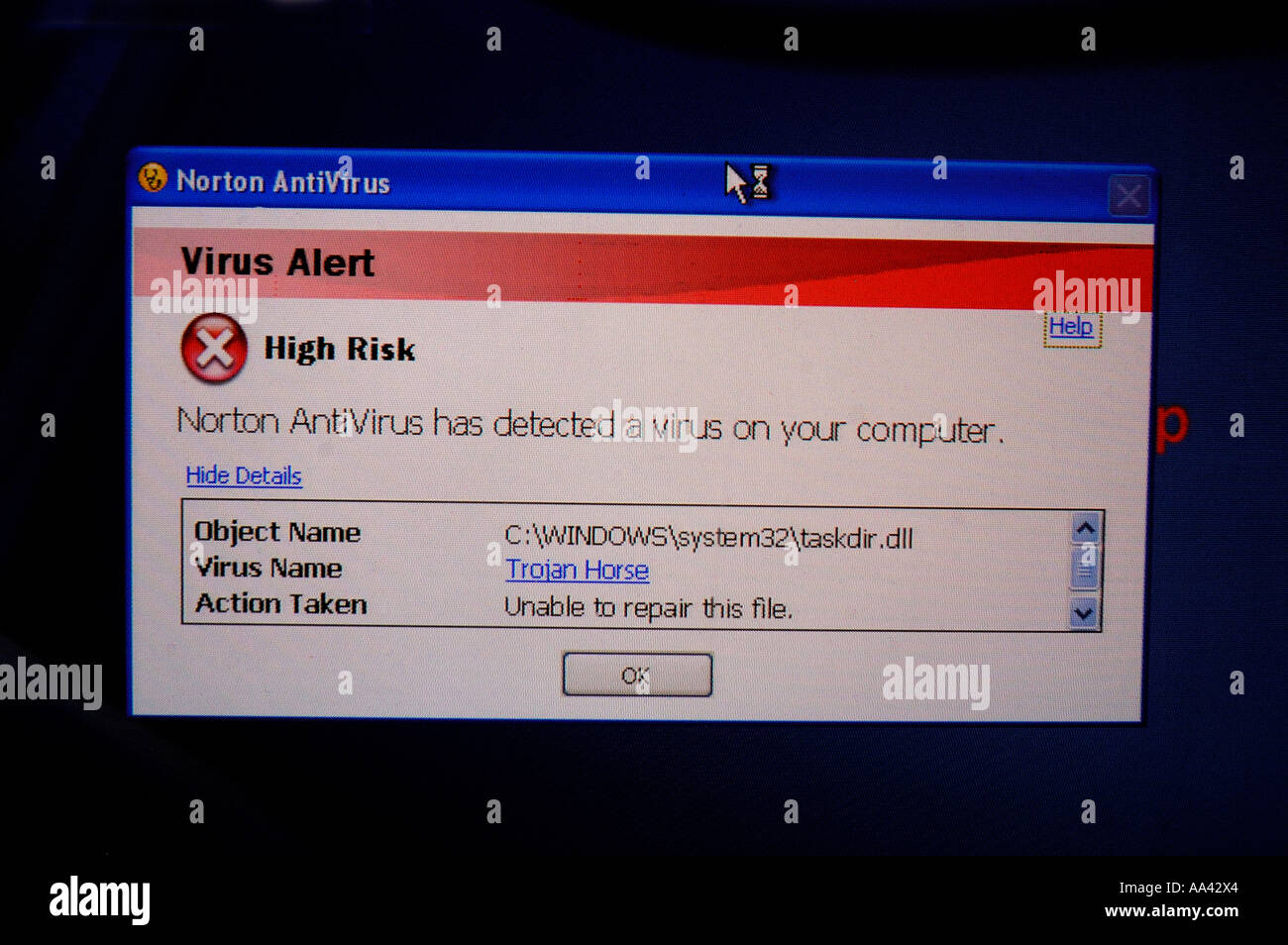 Norton Anti virus Trojan Horse warning
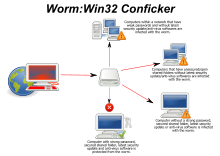
Norton Anti virus Trojan Horse warning  CCNA Security: Worm, Virus and Trojan
CCNA Security: Worm, Virus and Trojan  viruses, trojans and malicious software
viruses, trojans and malicious software  The Differences Between a Virus, Trojan
The Differences Between a Virus, Trojan  Computer Viruses, Worms and Trojans
Computer Viruses, Worms and Trojans  Ways To Prevent Trojan Horse Attacks
Ways To Prevent Trojan Horse Attacks  virus salami attack and trojan horse
virus salami attack and trojan horse  Trojan Virus | Terra Preta
Trojan Virus | Terra Preta 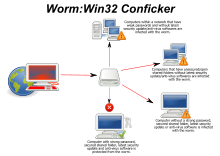 Computer worm - Wikipedia
Computer worm - Wikipedia  Trojan Viruses Spread and Detect
Trojan Viruses Spread and Detect  Cyber Attacks: Worms, Trojan Horse
Cyber Attacks: Worms, Trojan Horse  Computer Virus Spyware Trojan Horse
Computer Virus Spyware Trojan Horse  Computer Virus Trojan Malware Attack
Computer Virus Trojan Malware Attack  Trojan Horse Examples \u0026 How to Defend
Trojan Horse Examples \u0026 How to Defend  Virus,Worm,Trojan,Backdoor \u0026 Antivirus
Virus,Worm,Trojan,Backdoor \u0026 Antivirus  Computer Trojan Horse Virus Information
Computer Trojan Horse Virus Information
ISIS Militants Launch Counter-Attack on U.S.-Backed Forces in Northern Syria trojan virus attack Boy’s Body Found After He Was Dragged Into Water by Alligator at Disney World trojan virus attack Quora Question: What Would India do if Pakistan and Bangladesh Merged trojan virus attack As ISIS Attacks Mount, Turkey Steps Up Its War on Free Speech trojan virus attack
trojan virus attack Gold White Black Red Blue Beige Grey Price Rose Orange Purple Green Yellow Cyan Bordeaux pink Indigo Brown Silver