Trojan horse and malware protection
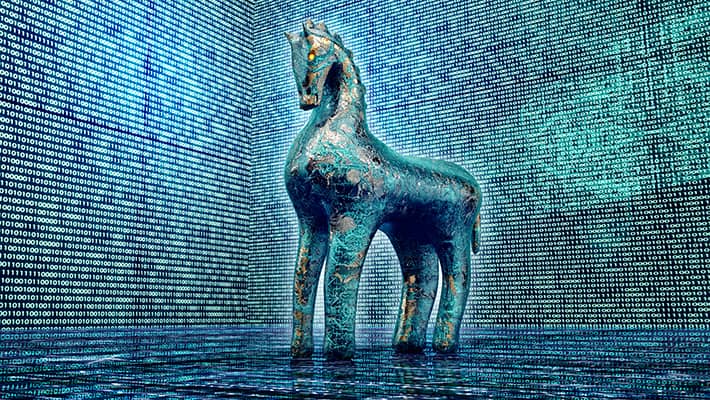
 The-Most-Common-Types-of-Malware-Trojan
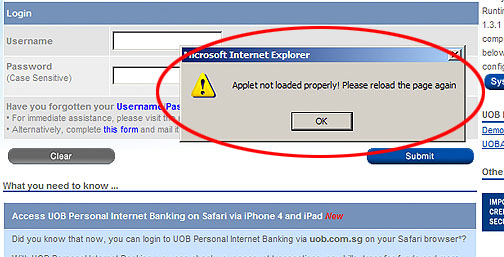
The-Most-Common-Types-of-Malware-Trojan 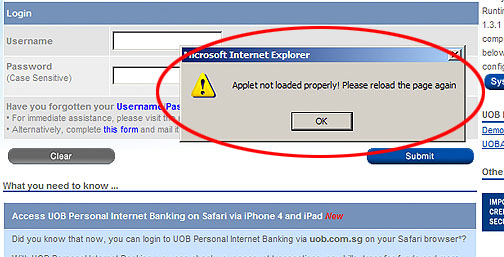 Trojan Horse malware targeting Local Banks
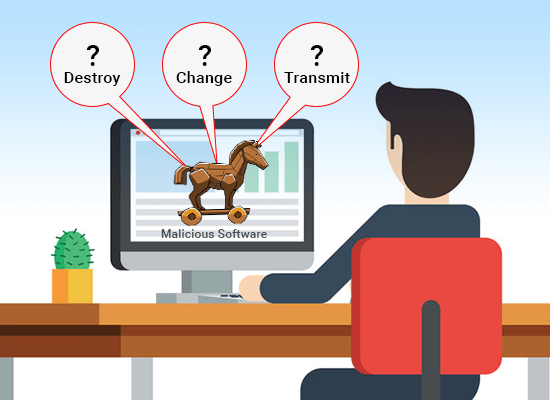
Trojan Horse malware targeting Local Banks  What is a Trojan Horse malware - how to
What is a Trojan Horse malware - how to  How to spot a Trojan horse virus — and
How to spot a Trojan horse virus — and  Malware, spyware, trojan, trojan horse
Malware, spyware, trojan, trojan horse  What is a Trojan Horse Virus? | How to
What is a Trojan Horse Virus? | How to  Trojan horse malware can completely
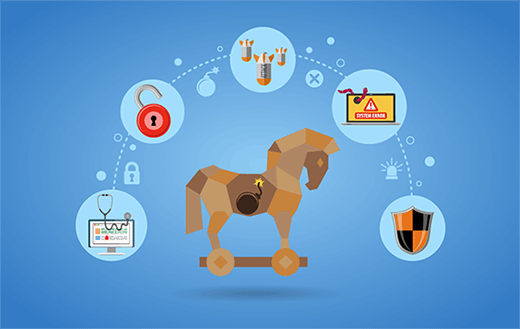
Trojan horse malware can completely  Cyber Attacks: Worms, Trojan Horse
Cyber Attacks: Worms, Trojan Horse  What is a Trojan Horse Virus
What is a Trojan Horse Virus  Dismantling the Trojan Horse
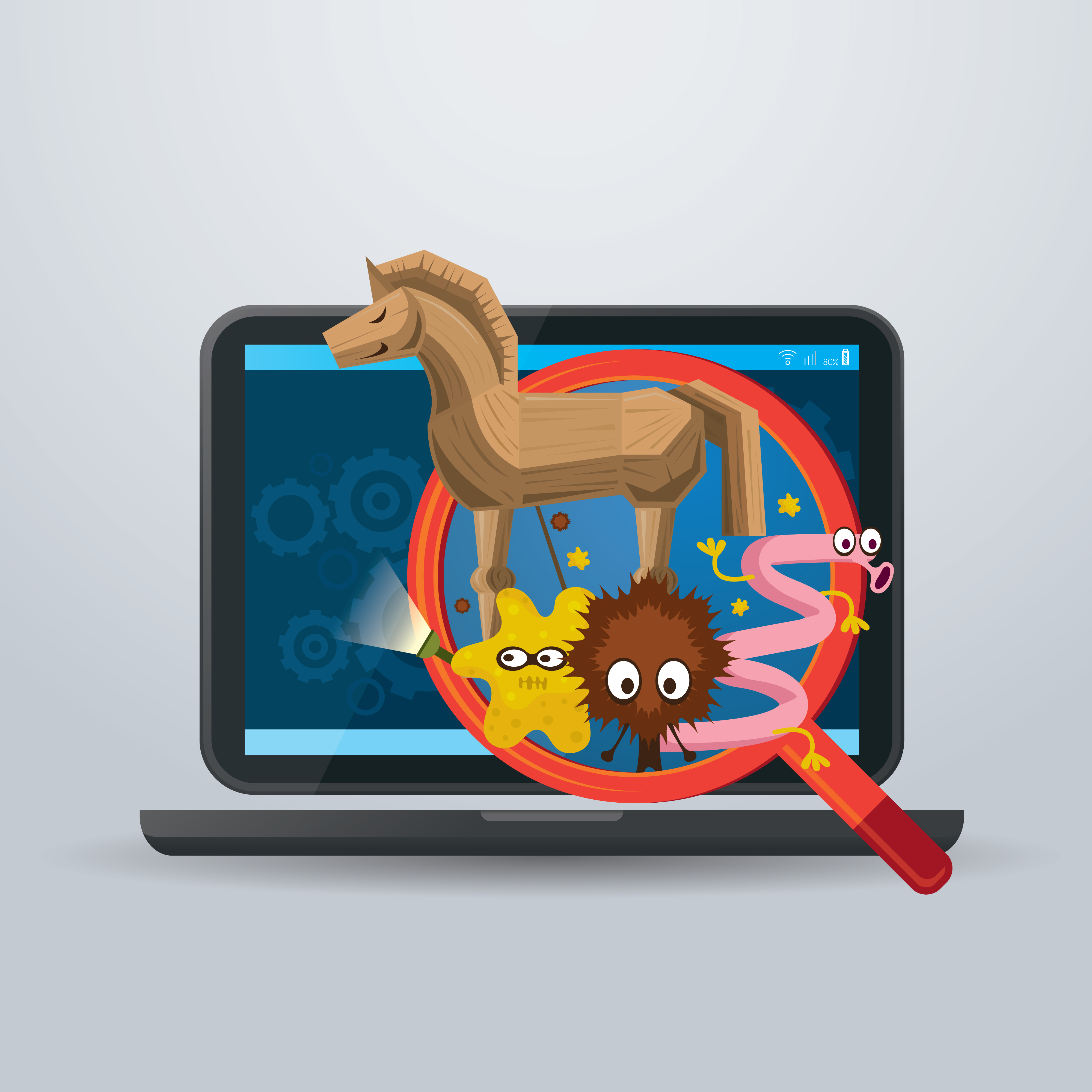
Dismantling the Trojan Horse  Malware, Trojan, Virus, and Worm
Malware, Trojan, Virus, and Worm  360 Total Security
360 Total Security  Trojan horse, Malware removal
Trojan horse, Malware removal  malware, Trojan, Phishing, and hacking
malware, Trojan, Phishing, and hacking  Computer Trojan Horse Malware Or Any
Computer Trojan Horse Malware Or Any  Computer Viruses, Worms and Trojans
Computer Viruses, Worms and Trojans  Trojan malware
Trojan malware  No Trojan Horse Malware Virus Computer
No Trojan Horse Malware Virus Computer  Trojan Horse Malware Effects On
Trojan Horse Malware Effects On  Trojan Horse Malware
Trojan Horse Malware  Trojan Horse malware targeting Local Banks
Trojan Horse malware targeting Local Banks  Malware Antivirus Software Transparent PNG
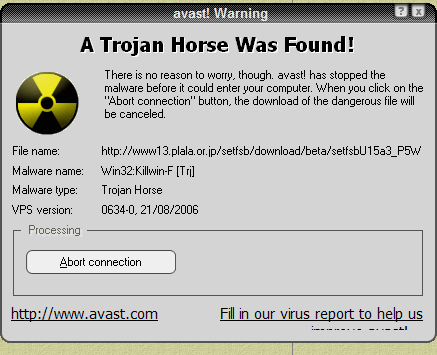
Malware Antivirus Software Transparent PNG  trojan horse malware example | Cyber
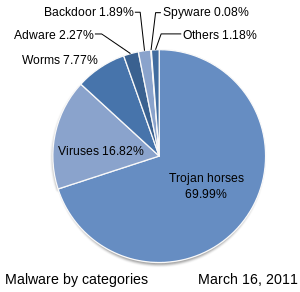
trojan horse malware example | Cyber  Malware
Malware  Trojan horse Malware Computer Icons
Trojan horse Malware Computer Icons 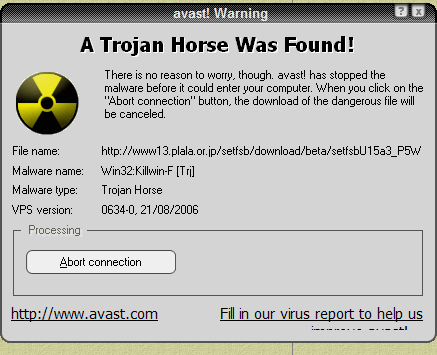 BlackEnergy - the most dangerous virus
BlackEnergy - the most dangerous virus  No Trojan Horse Vector \u0026 Photo (Free
No Trojan Horse Vector \u0026 Photo (Free  Trojan Horse—What Is It? Virus or
Trojan Horse—What Is It? Virus or  What is Malware? - Definition from
What is Malware? - Definition from 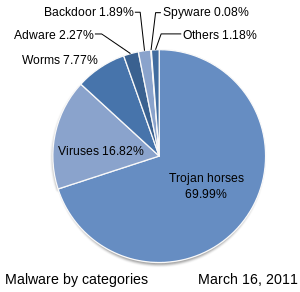 Malware - Wikipedia
Malware - Wikipedia  Explain A Trojan Horse To A Five-year-old
Explain A Trojan Horse To A Five-year-old  Common Malware Types: Vulnerability
Common Malware Types: Vulnerability  Malware Trojan horse, Hazard Sign s PNG
Malware Trojan horse, Hazard Sign s PNG  Trojan Horse Examples \u0026 How to Defend
Trojan Horse Examples \u0026 How to Defend  Trojan Horse Malware Computer Virus On
Trojan Horse Malware Computer Virus On
RAF Marham Attackers 'Seen Speeding Through Village' A Week Before Attempted Abduction what is trojan horse malware Why, Despite His Insults, the Chinese Love Trump what is trojan horse malware Spalding Shooting: Three Dead After Gun Attack in Lincolnshire, England what is trojan horse malware ISIS-Claimed Car Bomb Kills at Least 50 in Shiite District of Baghdad what is trojan horse malware
what is trojan horse malware Gold White Black Red Blue Beige Grey Price Rose Orange Purple Green Yellow Cyan Bordeaux pink Indigo Brown Silver






























/sitting-exercise-ball-Darren-Robb-Stockbyte-Getty-200254041-001-56a9db5d3df78cf772ab1c6b.jpg)